CDS340
|
FTP & SFTP File Transfer |
Last Revised: 10/27/22 |
This called routine can be used on Unix/Linux systems to communicate using ftp (File Transfer Protocol) or sftp (Secure File Transfer Protocol). It supports most popular ftp commands. The remote server can be any supported operating system including Unix, AIX, Linux, Windows, etc. CDS340 also supports the pubnet Value Added Network (VAN) which is similar to ftp.
Calling Format:
CALL "CDS340", ERR=XXXX, CHAN, CMD${, MSG$, DEBUG}
{Braces indicate optional parameters}.
ERR=
|
CDS340 exits with an error whenever the requested command fails.
This would include reasons such as unable to login, requested file to get is
not found, unable to perform a directory command, etc., or if the command
timed out with no reply from the remote ftp server. The MSG$
will contain the last ftp status message which may help determine the
problem. |
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
CHAN
|
Used as the channel for the connection to the ftp command, assigned by
CDS340 during the initial call to Open the ftp channel. The channel is
closed by CDS340 upon receipt of the Q command. |
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
CMD$
|
Command and arguments passed to CDS340. The first character
of CMD$ is the command type. Any additional characters
are arguments. Multiple arguments are separated by commas.
Commas cannot be used in any arguments.
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
MSG$
|
Returned from CDS340. In most cases, MSG$ will
contain the last ftp status message. In the case of the D command for
directory list, MSG$ will be templated. If no
non-directory files match the pattern then MSG$ will contain
only the CNT field and MSG.CNT will be zero.
If there are non-directory files that match the pattern specified, then
MSG$ will contain the fields listed below.
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
DEBUG
|
This optional parameter can be passed as 1 to request that CDS340
display all ftp status messages and prompt before exiting. Pass as a 2
to disable prompting the operator with an error message. This is the
default for background tasks. |
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Creating key files
The secure ftp protocol does not allow passing the password to the remote server. Although sftp will allow the user to enter the password, this is not very convenient when it is desired to automate an sftp process. Instead, you can generate key files, and save the public key on the remote server. When these key files are in place, then sftp will function without the need to manually enter the password.
Use the following command on linux servers to create both the public and private key files in the current user's home directory. The command may differ on other operating systems.
ssh-keygen -t rsa
You will be prompted for a passphrase. You should just touch Enter and not assign a passphrase. If you do assign a passphrase then you will need to enter it manually when making a connection.
The files created will be:
~/.ssh/id_rsa
~/.ssh/id_rsa.pub
The first file is the private key. The permissions must be r--r--r-- or rw-------. In the default location, the
private key can only be used by the user that created the file. This is
because the permissions of the .ssh directory is rwx------
which prevents others from accessing the private key. To share this
private key among multiple users, move the private key file to a directory
accessible by all users and insure the file permissions enable reading but not
writing.
The second file with the .pub extension is the public key. The contents of this file is required on the remote server in order to permit sftp connections without manually entering the password.
If the remote server is a linux server, then the content of your public key file needs to be appended to the
~/.ssh/authorized_keys file. In some cases, you can sftp or
scp the public key file to the remote server yourself. In other cases, you
will need to email the public key to the remote server administrator who will install you public key as appropriate for what ever operating system the remote server happens to be using. The permissions of the .ssh directory need to be rwx------ and the permissions of the authorized_keys file
must be rw-------.
If the remote server is a Microsoft Windows server, then create the .ssh folder in the Windows account profile folder, i.e., C:\Users\USERNAME\.ssh then define a file name authorized_keys with the contents of the contents of the public key file. Then grant read permissions to the .ssh folder. As an Administrator execute this command: icacls C:\Users\USERNAME\.ssh /grant "NT Service\sshd:R" /T
Note that the authorized_keys file whether linux or Windows, can contain multiple keys when required.
| Example |
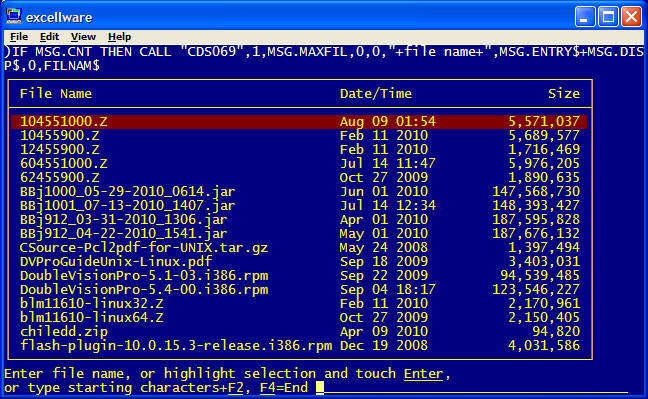
CALL "CDS340",ERR=FAIL,CHAN,"Oftp.excellware.com,username,password",MSG$CDS069 display will look like this:
|